Understanding the Threats of Apply Aims Deprived Cyber Cracksibile
The increasing reliance on digital technologies has led to a surge in cybercrimes, with perpetrators exploiting vulnerabilities in computer systems and networks to gain unauthorized access, steal sensitive information, and disrupt services. The concept of "apply aims deprived cyber cracksibile" is a critical aspect of understanding these threats and the need for robust cybersecurity measures to protect individuals, organizations, and nations from the scourge of cybercrime.
What is Cybercrime?
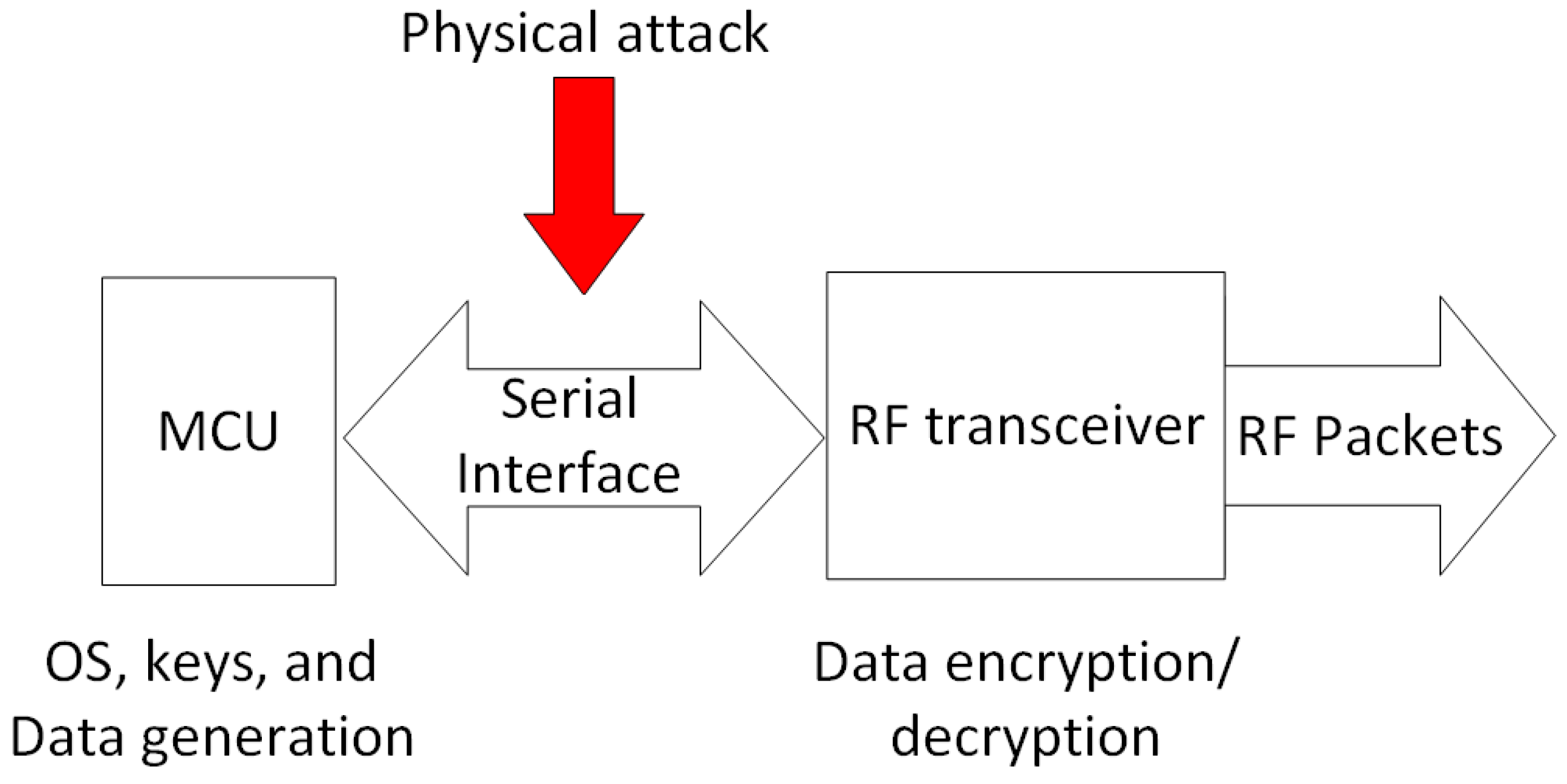
Cybercrime encompasses a wide range of criminal activities that are carried out using digital devices and/or networks. It includes hacking, phishing, identity theft, and denial-of-service (DoS) attacks, among others. Cybercriminals may exploit vulnerabilities in computer systems and networks to gain unauthorized access, steal sensitive information, disrupt services, and cause financial or reputational harm to their victims.

The Risks of Cybercrime
The risks of cybercrime are numerous and far-reaching. Cyberattacks can compromise sensitive information, disrupt critical infrastructure, and undermine the economy. The consequences of a cyberattack can be devastating, including financial losses, damage to reputation, and loss of customer trust. Moreover, cybercrime can have a profound impact on individuals, causing emotional distress, financial hardship, and even physical harm.
Understanding what motivates cybercriminals is a crucial part of improving our defenses against a barrage of cyberattacks. Cybercriminals are driven by a variety of motivations, including financial gain, personal satisfaction, and a desire for notoriety. By understanding these motivations, we can develop effective strategies to prevent and respond to cybercrimes.

Such details provide a deeper understanding and appreciation for Apply Aims Deprived Cyber Cracksibile.
Organizations and individuals can take a number of steps to protect themselves from cybercrime. These include implementing robust security protocols, conducting regular vulnerability assessments, and providing employees with cybersecurity training. Additionally, organizations can apply for cybersecurity certifications, such as the CISA (Certified Information Systems Security Professional) certification, to demonstrate their commitment to cybersecurity.
The Importance of Cybersecurity Certification
Cybersecurity certification is an essential aspect of protecting networks and computer hardware from unwanted threats and damages. Organizations that apply for cybersecurity certifications, such as the CISA certification, demonstrate their commitment to cybersecurity and their ability to protect sensitive information. Cybersecurity certification also provides individuals with the skills and knowledge they need to prevent and respond to cybercrimes.
This particular example perfectly highlights why Apply Aims Deprived Cyber Cracksibile is so captivating.
Cybersecurity Education and Training
Cybersecurity education and training are critical components of a robust cybersecurity strategy. By providing employees with cybersecurity training and education, organizations can empower them to make informed decisions about cybersecurity and protect sensitive information. Additionally, cybersecurity education and training can help to identify and mitigate cybersecurity risks before they become major problems.
Conclusion
The apply aims deprived cyber cracksibile is a critical concept in understanding the threats of cybercrime. By understanding the motivations of cybercriminals, implementing robust cybersecurity measures, and providing employees with cybersecurity education and training, we can protect ourselves from the scourge of cybercrime. Moreover, cybersecurity certification is an essential aspect of protecting networks and computer hardware from unwanted threats and damages. By applying for cybersecurity certifications, such as the CISA certification, organizations can demonstrate their commitment to cybersecurity and their ability to protect sensitive information.